The Timeline of Security and The Secret to Why Cybersecurity Sometimes Fails
By Chris Nyhuis, Vigilant CEO
A Vigilant Know More Series
We all know cyberattacks from sophisticated threat actors are at an all-time high. What the industry generally doesn’t understand is with the cybersecurity industry continuously improving, why are companies still getting hacked without knowing it? Vigilant is sharing our insight into this matter to help ensure your organization understands some of the potential reasons for cybersecurity failure, as well as the keys to cybersecurity success.
Reason #1 for Failure
Hackers Have Access to Many of Your Security Tools
Many of the security solutions, tools and technologies that companies put their faith in can actually be bought online. We like to call this “credit card security,” since security can often times be bought with a credit card. The reason this is dangerous is very simple: If you can purchase cybersecurity and deploy it within your environment – so can the very same threat actors you’re fighting against.
Open-sourced tech is certain to fail since threat actors have already purchased it and tested it in their own labs (Yes, hackers have labs). After mastering the ins-and-outs of the technology, and determining they can operate un-detected within it, they are ready to launch all types of attacks against you.
An easy to remember rule is: “Easily Accessible to Organizations = Easily Identifiable by Hackers.” Your first-line of defense can never be something you (or anyone else) can simply purchase online.
Reason #2 for Failure
“Checklist Security”
Another major reason why cybersecurity sometimes fails is due to what we call “Checklist Security.” Many compliance-heavy organizations (i.e. healthcare, etc.) follow a rigorous compliance checklist. The problem is that threat actors in your environment have the same checklist, too.
The other issue is that compliance-heavy organizations tend to focus primarily on vulnerability and pen testing assessments first, which are preventative measures. While these security measures reduce risk, improving detection should always be your first step. That’s because great detection will lower your cost of compliance and the speed of rolling it out since it will make your process driven by data instead of using a checklist that an external entity provided to you who knows nothing about your organization. YOU are responsible for your own security, and you know yourself better than anyone else.
Hackers win because they know their targets better than their targets know themselves. The easy-to-remember rule here is: detection first. Make decisions from what you learn and then implement additional controls. Being compliant is not the same as being secure. Fully compliant organizations are breached all the time – and it is only after the dust settles that they realize the hackers not only remained following multiple audits – but that they had been there for months.
The 212-Day Window
For most organizations, it takes five or six months to work down their checklist – potentially putting the company six months behind a threat actor. This can add up to a thirteen-month head start for threat actors.
Today’s threat actors develop malicious programs that are not only capable of effective infiltration but also remaining undetected for weeks, months, or in some cases, even years before they are detected and contained. This means that despite how strong your security solutions are at monitoring real-time activity, numbers show that an average intrusion can last for up to 212 days before even initial detection, much less remediation. During that 212-Day Window, cybercriminals collect enormous amounts of sensitive information and other business-related data, explore the organization, and prepare themselves for next steps (such as encryption).
This can have a significant impact on your business because by the time the technologies in your environment find a threat and notify you that it exists – 212 days have already gone by undetected, and they are long gone. Think of all the damage that can be done in 212 days.
Timeline of Security
You need your new security tools and technology fully operational... yesterday. Hackers are fast, organizations tend not to be. When I speak at events around the U.S., I poll audiences and have found that the average time organizations take to deploy technology is nine months. That is way too long. At Vigilant, we call this the Timeline of Security. It is the length of time it takes to choose, deploy, and make fully operational any technology or tool to ensure that it meets its intended purpose.
To illustrate the Timeline of Security, consider the cybersecurity tools and technology deployment process in an organization from the perspective of a 15 month timeline:
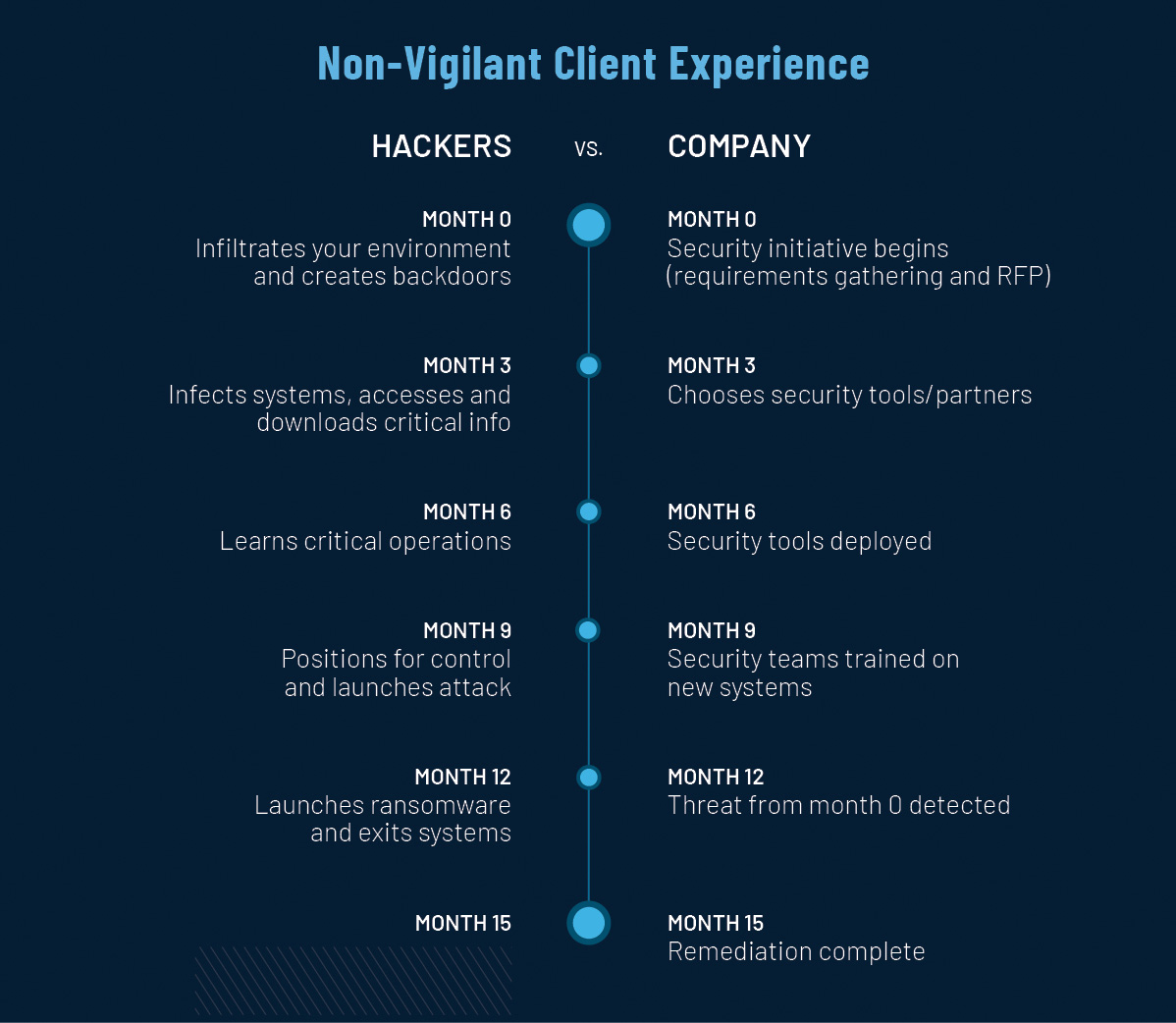
The above 15 month timeline is the typical timeline your organization will face vs. the timeline the hacker operates on. Your organization hasn’t even detected the threat until the hacker has launched ransomware and exits the system - this is 12 months after your security initiative began. To operate ahead of the speed of the hacker, your organization needs to be on the ideal optimized timeline.
The Ideal Optimized Timeline:
Month 0: A compliance (or security) initiative begins
Month 1: A detection solution is chosen and deployed
Month 2: Threats are detected
Month 3: Threats are remediated – narrowing the typical security timeline from 15 months to three months.
Vigilant's Top Recommendations for Orgs
Protect with proprietary tools and technologies that are not readily available to the public
The technology you choose should not be difficult or complex – it should be deployable quickly and easily. The more complex the technology – the more human error is likely to occur and the longer it takes to set up delaying the timeline more.
Break the 212-Day Window: A good rule of thumb is that you should be able to deploy two sites within the same day. Vigilant detects threats within hours not days. That’s a lot faster than the average – and it's only possible because we do things the right way – by ensuring our tools and technologies are not readily available to the public .
Most important: from a strategy process, you have to start with Detection first (not checklists or compliance products). You will save money because your entire compliance process will be faster and more efficient/affordable from a resources perspective – and you’ll find threat actors earlier.
A bad security decision today can take you out of business tomorrow. To learn more about how to avoid security failures by making detection a priority, the Vigilant team is always happy to chat with – and mostly listen – to you about your overall security infrastructure.